Evolving Cyber Defense Strategies
Cybercrime armies infiltrate digital ecosystems through hijacked devices,
silently transforming everyday tech into weapons of mass disruption.
These zombie networks execute coordinated strikes ranging from
server-crushing traffic floods to sophisticated ad fraud schemes.
Modern defense systems deploy multi-layered shields against automated invaders.
Traffic fingerprinting identifies robotic patterns within network streams,
while behavioral AI learns normal user rhythms to spot anomalies.
Geo-fencing blocks high-risk regions, and challenge protocols
separate human visitors from scripted imposters.
Leading cyber sentinels offer specialized protection:
Cloudflare's global threat radar analyzes traffic across 25M+ properties,
categorizing bots by malicious intent. ManageEngine's dual-threat hunters
(Log360 and NetFlow Analyzer) combine endpoint surveillance with
network flow diagnostics across Windows and Linux environments.
API guardians like Radware install digital bouncers that
vet incoming requests through customizable security policies.
SolarWinds takes an on-premise fortress approach, creating
virtual strongholds against device hijacking and firewall penetration.
Ad fraud specialists like ClickCease deploy click forensics,
dissecting engagement patterns to filter artificial interactions.
Meanwhile, Datadome's AI-powered screening operates transparently,
approving legitimate traffic without proxy bottlenecks.
Proactive mitigation strategies outweigh passive detection:
Overprovisioned server buffers absorb DDoS barrages while
decoy networks (honeypots) misdirect and analyze attackers.
IP reputation databases automatically block known malicious actors,
and traffic rerouting techniques nullify coordination between bots.
Evaluation priorities for cyber defense systems should emphasize:
1) Preemptive strike prevention against service outages
2) Multi-functional security integration beyond basic bot detection
3) Automated countermeasures that reduce attack impact
4) Real-time threat intelligence feeds with dynamic blocklists
5) Rapid response capabilities measured in seconds, not hours
Modern solutions cater to diverse infrastructure needs:
Cloud-based services offer instant deployment and infinite scaling,
while on-premise installations provide localized control.
Hybrid models blend subscription threat intelligence with
perpetual license options for budget flexibility.
The battlefield evolves as botnets adopt AI tactics,
making adaptive machine learning defenses critical.
Future-proof protection requires continuous protocol updates and
cross-platform visibility into web servers, APIs, and mobile interfaces.
ManageEngine Log360 is a comprehensive suite of security tools designed to monitor and respond to various threats, including botnets. The core of this package is a Security Information and Event Management (SIEM) system that collects log data from across your network and cloud accounts. This SIEM receives a threat intelligence feed, which includes a blacklist of IP addresses and domains known for malicious activities, such as botnet command and control (C&C) servers.
Key Features:
- Threat Intelligence Feed: Utilizes a continuous feed to blacklist malicious IP addresses and domains.
- Anomaly Detection: Analyzes system behavior to identify and flag unusual activities as potential threats.
- Network Monitoring: Continuously monitors network traffic to detect and alert on any anomalies.
- User Activity Tracking: Logs and tracks user actions to ensure security and compliance.
Log360 employs multiple methods to detect and block botnet activity, creating a multi-layered defense. By combining log analysis with network traffic monitoring, it can effectively identify and neutralize botnets. For instance, if a program is communicating excessively over the internet, the SIEM will flag this as anomalous behavior and take action to shut it down.
The Log360 package also includes a Security Orchestration, Automation, and Response (SOAR) system. This SOAR system coordinates all the security units and third-party tools, enabling automated responses to detected threats. This integration makes managing the diverse tools in the Log360 suite more efficient.
Beyond botnet detection, Log360 offers additional security features such as data loss prevention, Active Directory protection and auditing, and insider threat protection. Many of these features enhance the speed of threat detection, whether they are software-based or manual. The User and Entity Behavior Analytics (UEBA) feature provides activity baselining and anomaly detection, which is crucial for identifying zero-day attacks.
Comprehensive Security Approach:
- Integrated Security: Combines log analysis and network monitoring for thorough botnet detection.
- Automated Responses: Capable of executing coordinated, automated actions against detected threats.
- Enhanced User Protection: Provides robust user account and Active Directory protection.
- Compliance Ready: Supports major regulations like PCI DSS, GDPR, and HIPAA.
- Management Complexity: Requires a dedicated team for effective utilization and management.
Log360 is an on-premises solution that installs on Windows Server. It is available for a 30-day free trial, allowing you to evaluate its capabilities before making a purchase.
Why Choose ManageEngine Log360?
- Multi-Layered Security: Offers a comprehensive approach to network security, enabling real-time detection and mitigation of botnet activity.
- Advanced Log Management: Uses machine learning and threat intelligence to analyze logs from various sources, quickly identifying abnormal traffic and access patterns.
- Unified Security View: Correlates security events from different network components, providing a holistic view of network activity.
- Real-Time Alerts: Ensures prompt notification of potential threats, enabling rapid response and reducing the time to mitigate an attack.
- Detailed Forensic Reports: Allows security teams to investigate past incidents and uncover the root cause of infections.
- Ease of Use and Scalability: Suitable for businesses of all sizes, offering a user-friendly and scalable platform.
Download: Get a 30-day free trial
Official Site: https://www.manageengine.com/log-management/download.html
OS: Windows Server or SaaS
A sophisticated network defense solution emerges as a strategic ally against evolving cyber threats
'
By harnessing deep packet inspection and behavioral analysis, this platform illuminates shadowy network activities often associated with coordinated cyber campaigns
'
Real-time traffic visualization transforms raw data flows into interactive heatmaps, revealing hidden patterns of malicious swarm activities through temporal analysis
'
The system employs adaptive protocol fingerprinting to distinguish legitimate services from covert command-and-control channels attempting to blend with normal traffic
'
Customizable alert thresholds enable organizations to balance detection sensitivity with operational noise reduction across distributed infrastructures
'
While lacking direct mitigation capabilities, the platform integrates with next-gen firewalls to enable automated policy enforcement against identified threat actors
'
Three-tier deployment models cater to different operational scales:
Proof-of-concept version for testing core functionality
Single-network implementation with enhanced forensic capabilities
Multi-site enterprise deployment featuring QoS policy orchestration and application recognition technologies
'
The interface prioritizes actionable intelligence through drill-down analytics, allowing network architects to trace anomalous patterns to specific network segments
'
Bandwidth governance tools enable dynamic traffic shaping, temporarily isolating compromised nodes while maintaining critical business operations
'
Advanced correlation engines cross-reference flow data with global threat feeds, identifying emerging botnet signatures through machine learning pattern recognition
'
Though optimized for enterprise-scale infrastructure, the architecture supports gradual scaling from departmental pilots to full network coverage
'
Trial versions provide risk-free evaluation of predictive threat modeling capabilities and automated reporting functions
'
Security teams benefit from historical attack reconstructions, enabling post-incident hardening of network perimeters against similar future campaigns
'
The solution particularly shines in complex environments requiring granular visibility into application-layer interactions and encrypted traffic analysis
'
Implementation considerations include resource requirements for full packet capture analysis and necessary staff training for interpreting advanced threat metrics
'
Ultimately serves as a force multiplier for existing security stacks rather than standalone protection, enhancing detection rates while reducing incident response timelines
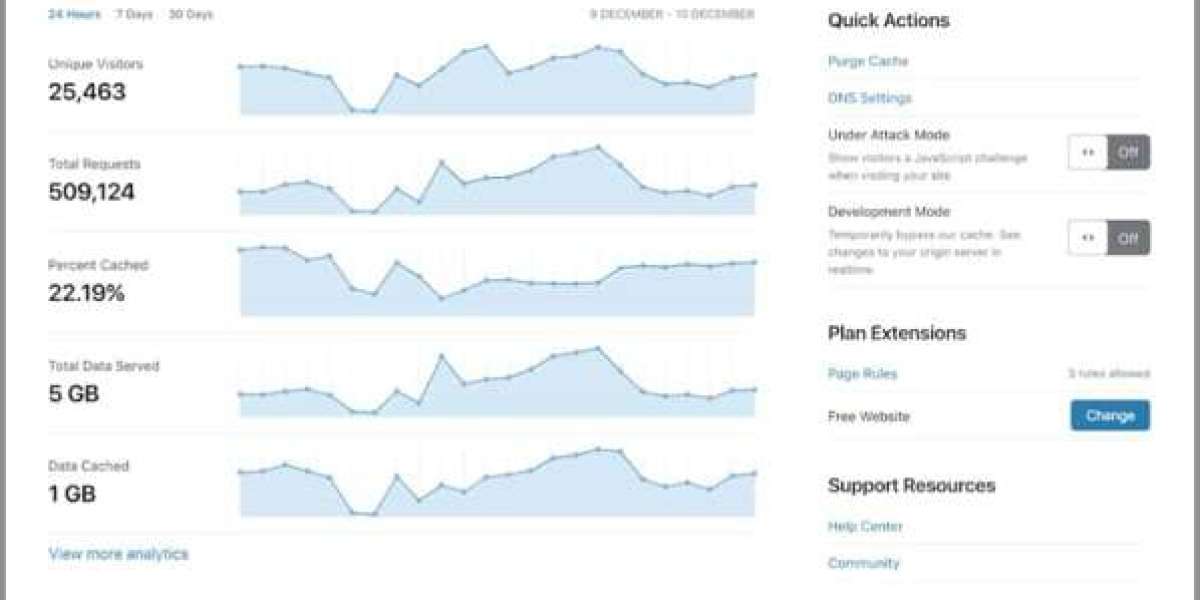
Cloudflare's Bot Protection Solutions
Cloudflare's Advanced Bot Protection Solutions
Cloudflare stands at the forefront of cybersecurity with its sophisticated bot detection and mitigation services. As a proxy-based edge service, Cloudflare shields networks by masking their actual IP addresses and filtering traffic through secure VPN connections.
The platform excels in identifying malicious automated traffic while allowing legitimate users to access protected resources. This capability is crucial in today's digital landscape where botnet attacks continue to evolve in complexity and scale.
Core Protection Capabilities
Cloudflare's solution goes far beyond basic DDoS protection. The comprehensive Bot Manager can identify and neutralize numerous automated threats including:
• Credential stuffing attempts targeting user accounts
• Content scraping operations that steal proprietary information
• Email account hijacking for spam distribution
• Fraudulent credit card transaction attempts
• Inventory manipulation that disrupts e-commerce operations
Security Infrastructure Benefits
The platform seamlessly integrates with content delivery networks to enhance both performance and security. Its robust traffic management system effectively handles massive traffic surges during attack scenarios, while SSL certificate integration ensures encrypted communications between users and protected websites.
Service Tiers and Accessibility
Cloudflare structures its offerings across four distinct service tiers:
• Free tier - Includes basic DDoS protection and essential security features
• Paid plans - Offer increasingly sophisticated protection capabilities
• Enterprise tier - Provides the complete Bot Manager solution with advanced detection methods
The company's reputation for reliability has fueled its significant growth in the cybersecurity sector. For small businesses and individual website owners, the free tier offers an accessible entry point to essential protection measures.
Leveraging Global Intelligence
A key strength of Cloudflare's approach is its utilization of vast network data to identify emerging threats. This global threat intelligence enables the system to accurately distinguish between legitimate users and malicious bots, reducing false positives while maintaining strong security posture.
While particularly effective for web-based assets, organizations should evaluate whether this solution adequately addresses their specific network protection requirements beyond web applications.
Radware Bot Manager is a versatile solution that can be deployed as an API, a plug-in, or even a virtual appliance. It offers multiple integration options including cloud server services, CDNs, and web servers, making it a flexible choice for various environments.
One of the key features of Radware Bot Manager is its ability to integrate seamlessly with Web Application Firewalls (WAFs) and Content Delivery Networks (CDNs), providing a robust defense against threats. The system also includes a unique proactive defense mechanism that allows for a direct counter-attack against bots, enhancing overall security.
In terms of fraud protection, Radware Bot Manager is designed to safeguard against a wide range of online fraud activities, ensuring your digital assets remain secure. This tool is part of a broader platform of edge services, focusing on the protection of web assets. Similar to Cloudflare, it can be combined with a WAF or CDN, but with the added advantage of being self-hosted as a virtual appliance, giving you more control over your security infrastructure.
When hosted on-premises, Radware Bot Manager cannot offload DDoS attacks. However, it can still filter traffic before it reaches your network and web servers by integrating with a WAF. The system meticulously analyzes incoming traffic, creating detailed profiles for each IP address to effectively track and identify bots.
To combat bot activity, Radware Bot Manager provides a range of automated actions. These include feeding fake data to bots to mislead them, challenging suspicious users with reCAPTCHA, or blocking access to confirmed bots. This comprehensive approach helps in maintaining the integrity of your website and protecting it from malicious activities.
Radware Bot Manager is suitable for businesses of all sizes, with the self-hosted version particularly appealing to larger enterprises. However, its DDoS mitigation capabilities are not as strong as those offered by competitors like Cloudflare. Additionally, the lack of a free tier makes it less attractive for small businesses.
The user interface of Radware Bot Manager is designed to be intuitive, with a dashboard that simplifies management and monitoring. It also offers granular traffic filtering, allowing for detailed analysis and control. Automated response options can be customized to suit your specific needs, providing a tailored security solution.
While Radware Bot Manager is a powerful tool, it would benefit from a longer trial period to allow for a more thorough evaluation. You can currently get a 15-day free trial to test its capabilities and see if it meets your security needs.
A virtualized instance deployed on VMware or Hyper-V platforms anchors SolarWinds’ network defense solution
Operating within isolated environments shields its monitoring engines from lateral network threats
Real-time traffic analysis combines with automated countermeasures like IP blocking and account freezes
Cross-platform compatibility extends to Windows, Linux, UNIX, and macOS environments for unified oversight
Integrated SIEM capabilities process firewall logs and endpoint data streams through behavioral analytics
Community-curated threat intelligence feeds dynamically update perimeter defenses with malicious IP registers
Compliance modules automate audit trails for HIPAA, PCI DSS, and SOX requirements through tamper-proof logging
Preconfigured detection rules accelerate threat identification across 700+ attack pattern templates
File integrity monitoring safeguards forensic data while smart reporting reduces false alert fatigue
On-premises deployment suits enterprise networks but may overwhelm smaller IT teams complexity-wise
Thirty-day evaluation period allows full testing of automated response workflows and log correlation features
Hybrid architecture balances immediate traffic interception with post-entry forensic investigation capabilities
Mid-sized to large organizations gain layered protection combining perimeter blocking with internal activity audits
Value proposition emerges from bundled threat prevention and compliance tools in single platform
Resource-intensive implementation demands dedicated Windows Server infrastructure for optimal performance
Click Fraud Prevention Solutions
Click fraud, a deceptive practice where bots generate excessive, unattended ad clicks, can significantly inflate an advertiser's bill. This technique is often employed by advertising agencies or competitors aiming to deplete the target's advertising credits before genuine users see the ads. ClickCease, a cloud-based solution, specializes in detecting and preventing such fraudulent activities, particularly on platforms like Google Ads.
Key Features:
- Cloud-Based Operation: The system operates entirely online, ensuring seamless integration and management.
- Fraud Prevention: It specifically targets and blocks click fraud, safeguarding advertisers from inflated costs.
- Competitor Insights: The tool helps identify and mitigate actions by competitors, providing valuable insights into their tactics.
ClickCease has carved out a niche in the bot detection market by focusing on click fraud protection. This tool is invaluable for disputing pay-per-click bills and securing Google Ads accounts against malicious rivals who might try to drive up your expenses. It also blocks IP addresses of known click farms, preventing them from accessing your site.
Various entities, including activists and large-scale click farms, may attempt to drain your ad budget. ClickCease combats this by using a JavaScript insert that you add to your website's code. This script gathers data on users who clicked on your ads and visited your site. It then builds profiles of these visitors, identifying those who are not real or are manually performing click fraud. When malicious activity is detected, ClickCease automatically adds the source IP address to the exclusion list in your Google Ads account.
The service offers additional utilities to help manage the Google Ads exclusion list, which has a limit of 500 IP addresses. Even if you lack technical expertise, ClickCease is user-friendly, with detailed instructions provided during the signup process.
Specialized Features:
- Click Fraud Detection: Highly effective at identifying and preventing fraudulent ad clicks, thereby saving advertising budgets.
- Automated IP Blocking: Automatically excludes malicious IP addresses from interacting with your ads.
- Simple Implementation: Easy to set up with a straightforward JavaScript insertion for website integration.
Considerations:
- Limited Scope: Focuses solely on click fraud, without broader network or DDoS protections.
- Trial Limitations: A longer trial period would be beneficial for more comprehensive evaluation.
ClickCease offers two plans: Standard for a single domain and Pro for unlimited domains. You can evaluate the service with a 7-day free trial.
Datadome stands out in the realm of botnet detection with its dual approach, combining scans for OWASP's top ten threats with robust botnet blocking. This solution not only identifies and mitigates botnet activities but also acts as a comprehensive vulnerability scanner.
Key Features:
- Comprehensive Protection: A cloud-based service that monitors and defends against botnet activities and payment fraud.
- Advanced Fraud Detection: Detects and prevents various forms of malicious behavior, such as scalping, inventory hoarding, and other bot-driven attacks.
- OWASP Awareness: Scans for and addresses vulnerabilities listed in the OWASP top ten, enhancing overall security.
- Bot Activity Detection: Identifies and mitigates a wide range of bot-driven threats, including DDoS attacks, scraping, account takeovers, and click fraud.
- Threat Intelligence Feed: Shares attack data across all customers, providing a more informed and proactive defense.
- Integration Flexibility: Easily integrates into websites, mobile apps, and services via a plugin, with data accessible through a cloud-based console.
- Intuitive Management Interface: Offers a user-friendly web interface for easy configuration, monitoring, and threat analysis.
Datadome is designed to protect both mobile apps and websites, making it a versatile solution. Unlike some competitors, Datadome is transparent about its pricing, which helps potential clients understand the cost and determine if it fits their budget. The service is capable of handling millions of connection requests per month, ensuring scalability and performance.
Pricing and Plans:
- Subscription Model: Datadome operates on a subscription basis, with three distinct plans: Starter, Business, and Corporate.
- Starter Plan: Priced at $1,590 per month, or $1,190 per month if paid annually. This plan primarily focuses on website protection.
- Business Plan: Offers additional features and higher capacity, suitable for larger organizations.
- Corporate Plan: The most comprehensive plan, covering mobile apps, APIs, and websites. It is priced at $7,790 per month, or $5,990 per month if paid annually.
While Datadome is an expensive option, it is tailored for large organizations with substantial budgets. The high cost reflects the advanced features and comprehensive protection it provides, making it a premium choice for those who prioritize robust security.
Reblaze Bot Management functions as a proxy server, filtering web traffic to ensure that only legitimate users are allowed through. Each connection request is processed in just 0.5 milliseconds, ensuring high-speed performance.
Key Features:
- Integrated Security: Reblaze combines with a Web Application Firewall (WAF) and Content Delivery Network (CDN) to provide comprehensive web protection.
- High-Speed Processing: The system analyzes and filters web traffic in a mere 0.5 milliseconds.
- Extensive Blacklisting: Utilizes a large database of known malicious sources to prevent scams and traffic floods.
- Efficient Traffic Filtration: Quickly and accurately differentiates between legitimate users and bots, maintaining optimal site performance.
- Comprehensive Web Protection: Offers an all-in-one security solution that includes bot management, DDoS mitigation, and content delivery acceleration.
- Advanced Bot Detection: Employs behavioral profiling to identify and block sophisticated botnet attacks.
- Cloud-Only Availability: Available exclusively in cloud environments, which may limit flexibility for some organizations.
Reblaze's bot management service is part of a broader bundle that includes a CDN and DDoS mitigation. One of its key strengths is the multi-layered traffic assessment system that does not compromise site response times. The platform uses a profiling strategy to detect automated bot systems, even if they switch IP addresses or use multiple zombie devices. It looks for specific indicators of suspicious activity to quickly identify potential bots.
The full Reblaze service also includes a WAF and a CDN, providing edge services that keep your website running smoothly. The botnet detection system operates through several rapid phases, ensuring quick and accurate identification of threats.
Reblaze is a strong competitor to Cloudflare, but it does not publish its pricing, which could lead to unexpected costs for those who start with the 30-day free trial. The platform is delivered from the cloud and includes activity reports and historical analysis support.
Botnets typically use many zombie computers to launch DDoS attacks, which have standard formats. Some DDoS attack strategies, like reflection attacks, are not common in botnet activity because the traffic volume from zombie computers is sufficient to overwhelm a web server. Bot detection systems focus on traffic patterns and packet structures rather than source addresses.
Bot detection software often operates within a firewall. If you opt for a botnet detection package, it should be deployed on a gateway router or a server that provides filtering services, such as a cloud-based firewall-as-a-service. These services operate at the network boundary, where bots direct traffic. Modern firewalls and proxy services generally include botnet protection.
Cloudflare stands out by offering one of the largest DDoS protection services globally. They maintain a list of botnet traffic sources but do not rely heavily on IP address blacklists, as individual zombie devices in a botnet are rarely reused. Instead, Cloudflare uses fingerprinting and selective challenges to filter out potential threats while allowing most traffic through.
What is a Netflix VPN and How to Get One
A Netflix VPN is a tool that enables viewers to bypass geographical restrictions and access a wider range of content by connecting to servers in various countries. By using this service, users can enjoy movies and TV shows that may not be available in their local Netflix library, enhancing their streaming experience.
Why Choose SafeShell as Your Netflix VPN?
If people want to access region-restricted content by Netflix unblocked , they may want to consider the SafeShell VPN . 1. One of the key benefits is its high-speed servers, which are specifically optimized for seamless Netflix streaming, ensuring uninterrupted and high-definition viewing. 2. SafeShell VPN also allows you to connect up to five devices simultaneously, supporting a wide range of operating systems such as Windows, macOS, iOS, Android, Apple TV, Android TV, and Apple Vision Pro. 3. The exclusive App Mode feature lets you unlock and enjoy content from multiple regions at the same time, providing a diverse range of streaming services and libraries. 4. With lightning-fast connection speeds and no bandwidth limitations, you can say goodbye to buffering and throttling. 5. Top-level security is ensured with the proprietary "ShellGuard" VPN protocol, advanced encryption, and robust security features, protecting your data and privacy. 6. Additionally, SafeShell VPN offers a flexible free trial plan, allowing users to explore its robust features without any commitment.
A Step-by-Step Guide to Watch Netflix with SafeShell VPN
To begin using SafeShell Netflix VPN for accessing global Netflix libraries, first ensure you’ve installed the application on your device. Navigate to the official SafeShell VPN platform, download the software compatible with your operating system, and complete the installation. Once launched, log in using your subscribed credentials and select the APP mode from the interface options, optimized for seamless streaming performance. This mode prioritizes speed and stability, crucial for uninterrupted binge-watching sessions.
Next, explore the server list within the SafeShell VPN app and pick a location matching the Netflix region you wish to unblock. After connecting to the server, open your Netflix app or browser, and log into your account. The platform will now display content exclusive to the selected region, thanks to the encrypted VPN tunnel. For optimal results, ensure your SafeShell Netflix VPN remains active throughout your streaming session to avoid geo-restriction errors.